For the past year or so, I’ve been watching some of my friends and mentors participate in bug bounty programs. The programs are offered by many websites and organizations, where individuals can receive recognition and monetary compensation for reporting bugs related to security flaws. I’ve been itching to participate in one for a while, but have felt that I didn’t know enough to actually participate and find anything. I had already realized my first few submissions were not going to be major payouts…but I was concerned I wasn’t going to be able to find anything at all.
After my trip to DEF CON and meeting up with some of my previously mentioned bug-hunting friends and mentors, as well as attending a few talks regarding the bug bounty space a little more, a co-workers and close mentor of mine and I decided to jump in and try to start doing bounties once we got home!
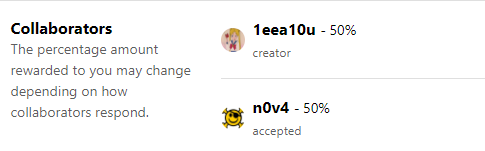
Before we could start hacking away though, we had to decide which program/service to use. The two most popular bug bounty programs the two of us saw at DEF CON were HackerOne and Bugcrowd. Both have a very similar base. They both act as a sort of “middle man” between company and hacker. They gather everything they need from the company in order to create a valid test, display it on their site, and then hackers can grab and go at whatever service they want to mess around with based on the stated criteria. My mentor n0v4 and I wanted to work together on this. We both have specific and varying skill-sets that can help us while testing. We wanted to split any and all rewards 50/50. One thing that Bugcrowd had that HackerOne did not is a collaborator, group, or team option. HackerOne does allow a group to work on one project and report together, but comes with a few things we did not like for what we wanted to accomplish…
- You had to manually divvy up payouts yourself
- Whoever submitted the final report would get the reputation for that finding and no one else.
- Taxes. Whoever the main collaborator/hacker on that bounty was would be stuck paying out any taxation on winnings as the compensation was 100% tied to them.
Bugcrowd offers this cool thing called collaboration. When you go to submit a report, you can choose numerous people that worked with you on that bounty and can split up winnings in any percentage right then and there.
After we made our accounts, we started digging though what we wanted to hack and came up with a small list of what ones we were going to tackle first. Bug Bounties are similar to a penetration test, as in you get a list of what targets are in/out of scope, specific focus areas, what things will NOT result in a payout (such as information disclosure or already known issues) and the proper way to create any sort of accounts needed for testing. They also tell you what type of payouts are expected based on the severity of certain vulnerabilities found. We also made sure that all of the bounties we would potentially take part in were a part of Safe Harbor.
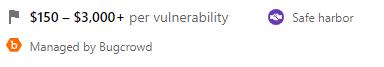
In short, Anti-hacking laws such as the Computer Fraud and Abuse Act (CFAA) are based on the idea that a hacker is always a malicious person by default, and does not make exceptions for bounty hunters and good-faith, “white hat” hackers to do their work safely. Until the laws change, there is need to create “band-aids” to bridge this legislative gap. Safe Harbor bug bounties protect good-faith hackers from different types of legal prosecution. The last thing my mentor and I need right now is a nasty run-in with the law, so we decided to stick with programs that were either Safe Harbor or Partial Safe Harbor.
You can read more about Bug Crowd’s stance on protecting their hackers here.
As of the writing of this post, n0v4 and I have submitted one report and have received no payouts yet. We are actively working on another one now and plan on attempting at least one bounty a week, if not more. Not only is the chance of getting a couple extra bucks thrown my way very lucrative (I have to pay my university tuition somehow), but I also hope to use my participation in these programs to help further develop and refine my penetration testing and report writing skills over the next couple of submissions!